Exclusive-128 Bit NLFSR Stream Cipher for Wireless Sensor Network Applications
Texto
Imagem
Documentos relacionados
This paper is organised as follows: in section II the seven-equation model is written and closure relations are given; the numerical method used is mentioned in section III; the
At this room ECG signals for every patient are measured using wireless nodes then these signals are transmitted to the nursing room for remote monitoring.. The nursing
The way the streams are reduced depends on the moment the reduction is going to be performed, i.e., during sensing or routing streams, and the type of data stream we are dealing
When the sensor stream size and number of nodes generating data vary we can observe the impact on the delay by using our solution.. Again, in the all cases, the sample of log n
This strategy considers three main aspects: (i) The design of real-time application to obtain the minimum deadlines; (ii) An analytic model to estimate the ideal sample size used
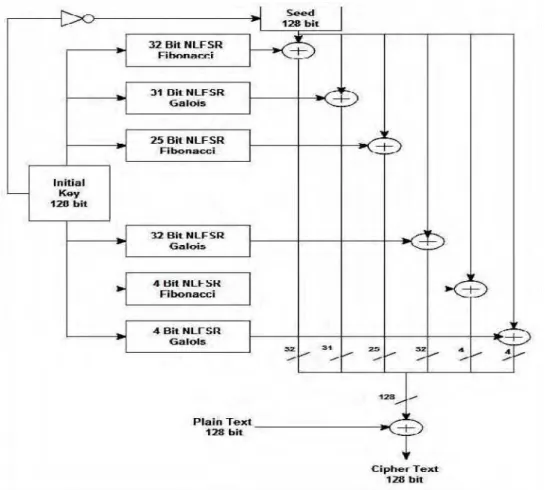
In this approach the encryption is simply adding the key to the plain text number to get the cipher text number while decryption is subtracting the key from the cipher text number
In this paper design the 4-bit Vedic multiplier using different adder and implementation 8-bit radix-2 FFT algorithm.. The paper is organized as follows: Section II
average value of bit stream at the output of Q2 during each sampling period namely β gives the discrete value of product of normalized samples of input signals (( x/n )×( y/n