Role of cloud computing in higher study
Texto
Imagem
Documentos relacionados
In this paper, after reviewing the literature on RFID in cloud environment, RFID is used in tracking and automatic identification is coalesced with cloud computing technique to
Optimal cloud security practices should include encryption of sensitive data used by cloud- based virtual machines; centralized key management that allows the user
This scenario may be interesting in scenarios of cooperation networks, it is noteworthy that combined with common interests, a cooperation network can share
I find that caps on individual contributions are associated with the convergence of platforms, whereas other commonly found measures, such as direct public funding, public disclosure
Indeed, it consists of transporting the course contents generated in the classroom managed by a private cloud computing towards its learning community managed by a public
each one of the nodes received/issued. We tested 3 scenarios where 100 subscriptions with computation were submitted with a specified input tag , and the number of nodes in the cell
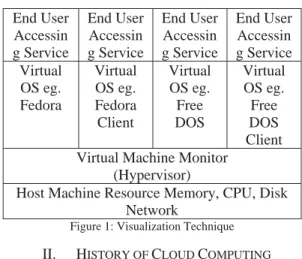
With this in mind, the cloud computing system (OpenStack) described in this chapter aims to provide the core features of a cloud computing architecture, On-demand self- service
Another problem in cloud computing is that huge amount of logs make the system administarator hard to analyse them.In this paper we proposed the method that enables cloud