Cloud Computing and Agricultural Development of China: Theory and Practice
Texto
Imagem

Documentos relacionados
Optimal cloud security practices should include encryption of sensitive data used by cloud- based virtual machines; centralized key management that allows the user
The probability of attending school four our group of interest in this region increased by 6.5 percentage points after the expansion of the Bolsa Família program in 2007 and
“Cloud” computing cyber infrastructure, and builds upon decades of research in virtualization, distributed computing, “grid computing”, utility computing, and, more
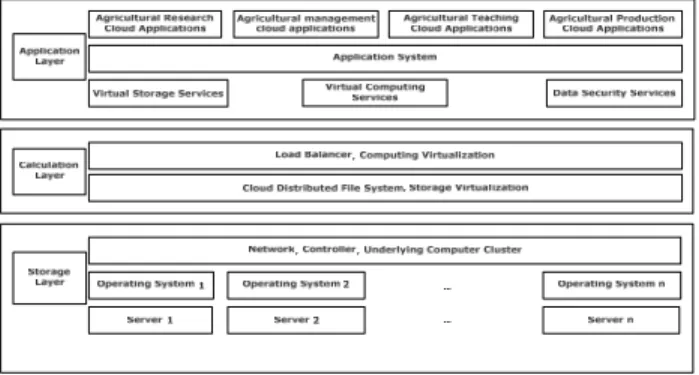
With this in mind, the cloud computing system (OpenStack) described in this chapter aims to provide the core features of a cloud computing architecture, On-demand self- service
Another problem in cloud computing is that huge amount of logs make the system administarator hard to analyse them.In this paper we proposed the method that enables cloud
The cloud computing security based on fully Homomorphic encryption, is a new concept of security which enables providing results of calculations on encrypted
Power demand of the mixer’s drive reveals the mixer’s operating characteristics and reliable monitoring of the mixing processes involving the evaluation of power consumption
According to NIST – “ Cloud Computing is a model for enabling ubiquitous, convenient, on-demand network access to a shared pool of configurable computing