A Secure Routing Protocol to Eliminate Integrity, Authentication and Sleep Deprivation Based Threats in Mobile Ad hoc Network
Texto
Imagem



Documentos relacionados
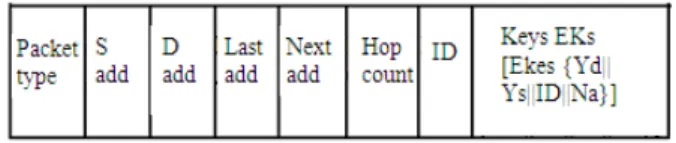
The proposed method states that the mobile nodes must be formed as groups for better security .It generates message authentication code during route discovery phase and then
if timeout period of sender node is x then timeout period of receiver node will be (x-m), where m will be critical factor. This factor [16] helps us to control the
In Case 1, i,e., for high level of security ( sec_ level = 1), during routing process, the source and destination nodes separately verify the authenticity of all other nodes in
If it is destination, it will accept the message and send acknowledgement to sender otherwise this node will send message to the node in its range that have
Earlier on-demand routing protocols[3,4,5,6,7] were based on flooding the routing packets in all directions irrespective of the location of the destination node, resulting
Wormhole attacks are organized in three different type namely closed, half open and open on the basis visibility of malicious node[10] in the route discover by routing
Finally, it is being observed that the proposed RBDS using GKM has efficiently desgined for an effective communication in MANET using Group Key management
Routing is the critical issue in the MANET and focus based on routing protocols such as Ad hoc On-demand Distance Routing Protocol (AODV), Dynamic Source Routing (DSR),


