ORAT FOR GREEN CLOUD COMPUTING
Texto
Imagem

Documentos relacionados
Optimal cloud security practices should include encryption of sensitive data used by cloud- based virtual machines; centralized key management that allows the user
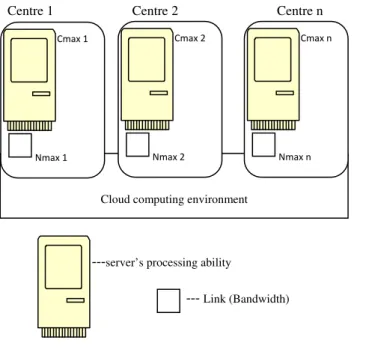
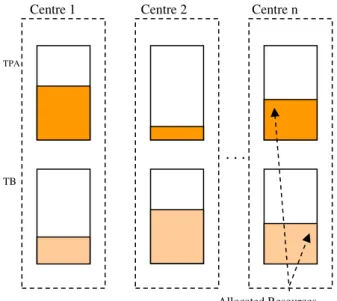
With this in mind, the cloud computing system (OpenStack) described in this chapter aims to provide the core features of a cloud computing architecture, On-demand self- service
Another variant of role-based access control proposed for cloud computing environments is the Attribute-role-based access control (ARBAC) model [9], wherein the data
Another problem in cloud computing is that huge amount of logs make the system administarator hard to analyse them.In this paper we proposed the method that enables cloud
Abstract. The emergence of the Internet as a ubiquitous means of communication fostered the growth of new business and service models based on Cloud Computing.
I find that caps on individual contributions are associated with the convergence of platforms, whereas other commonly found measures, such as direct public funding, public disclosure
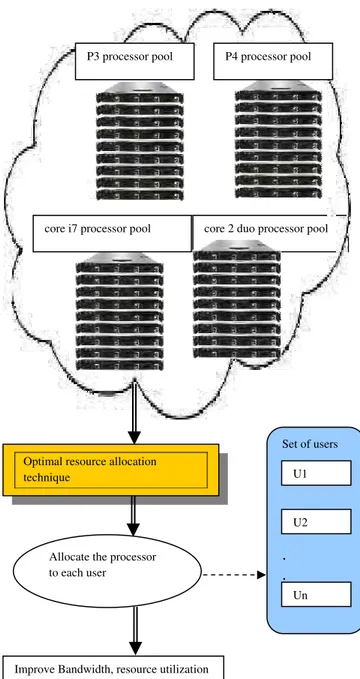
NIST [1] gives a basic definition of cloud computing as “a model for enabling conve nient, on-demand network access to a shared pool of configurable computing
The cloud computing security based on fully Homomorphic encryption, is a new concept of security which enables providing results of calculations on encrypted