Practical Isolated Searchable Encryption in a Trusted Computing Environment
Texto
Imagem

Documentos relacionados
The questionnaire has a number of branching points to differentiate among pilgrims who have walked the Camino, carried mobile devices while walking, carried smartphones
Along these lines, the objective of a safe deduplication framework is to give data security, against both inside and outside foes, with the space efficiency
Phospho-ERK expression was found to be higher in malignant tumors compared to benign tumors or normal adrenal glands, suggesting that MAPK/ERK pathway activation could
A SPE apresenta inúmeras vantagens relativamente a outras técnicas tradicionais de preparação de amostra, como a LLE, tais como: menor tempo de preparação de
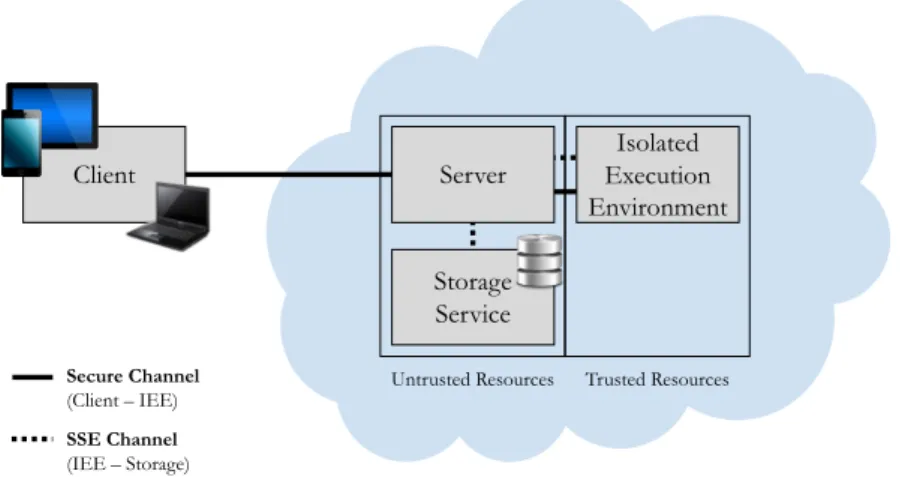
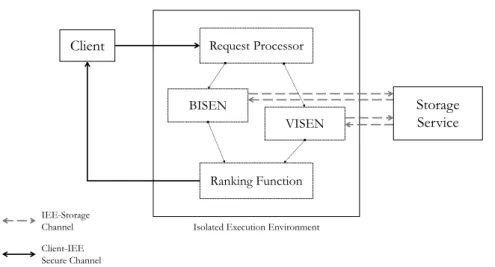
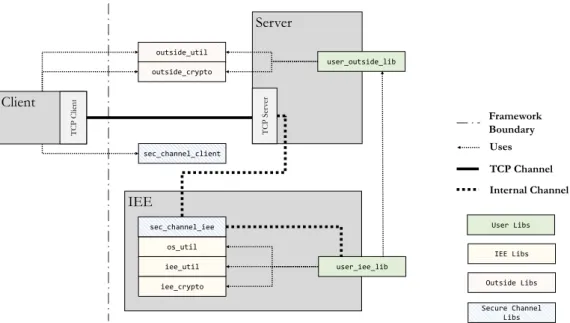
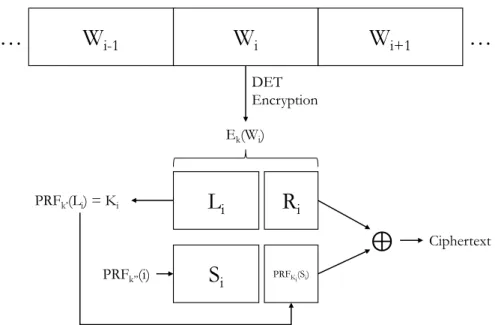
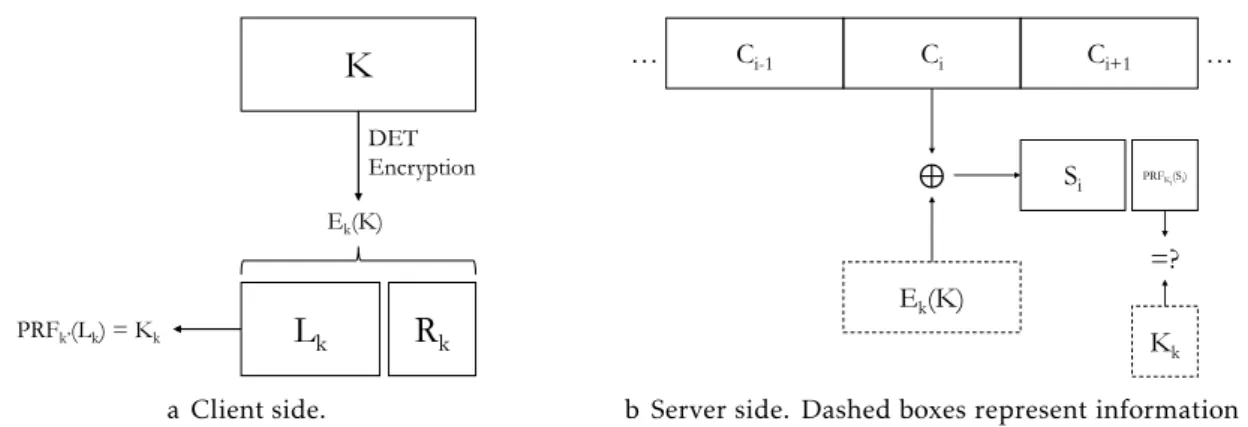
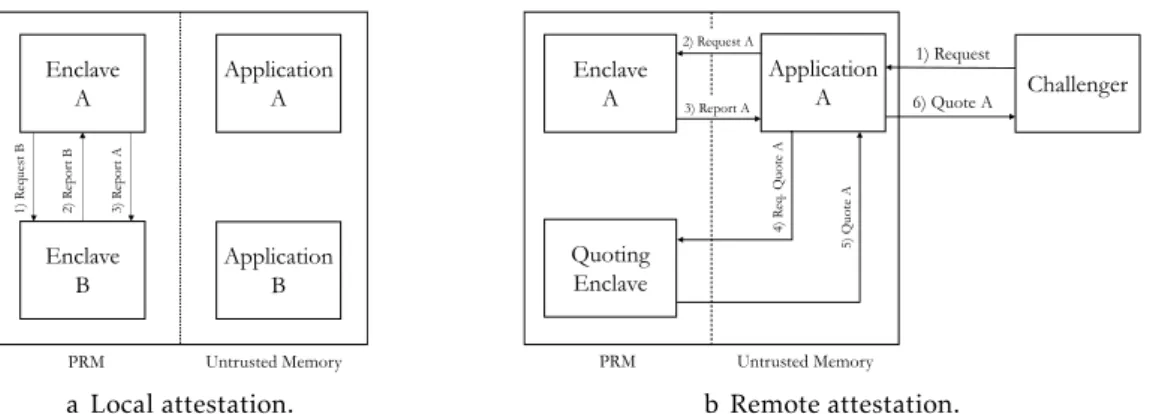
In this dissertation we focused primarily in providing privacy, availability and integrity of data stored in the provided multi-cloud storage backends, while allowing multi
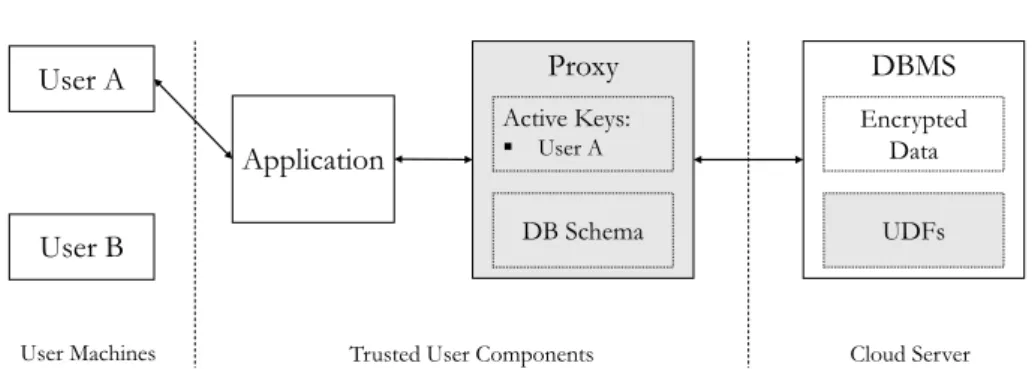
It shares massively scalable, elastic resources (e.g., data, calculations, and services) transparently among the users over a massive network [3]. These opportunities, however,
The remaining part of the paper is summarized as follows: Section 2 describes the problem statement, section 3 provides the clustering and build index algorithm, section
Since data owners and service providers are usually not in the same trusted domain in cloud computing, a new access control scheme employing attribute-based encryption is proposed