A Survey on Cloud Computing Security Issues, Vendor Evaluation and Selection Process: World Future Society
Texto
Imagem
Documentos relacionados
By using the homomorphic token with dispersed confirmation of deletion coded information, our plan accomplishes the capacity rightness protection and information
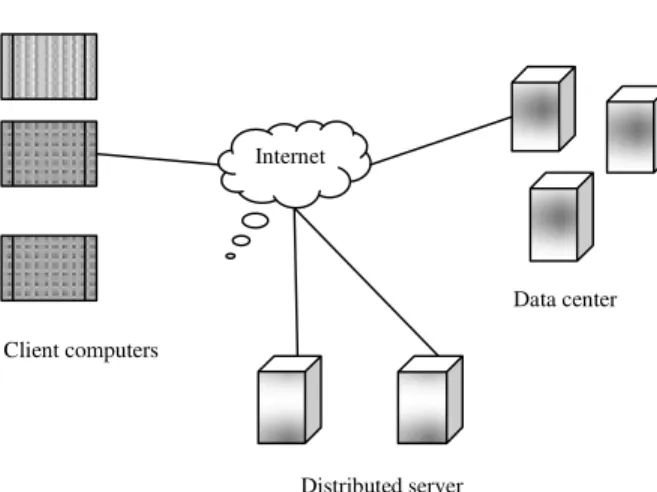
“Cloud” computing cyber infrastructure, and builds upon decades of research in virtualization, distributed computing, “grid computing”, utility computing, and, more
Cloud computing providers offer services built around three fundamental models: Infrastructure as a service (IaaS), platform as a service (PaaS), and software as a service
Amazon VPC enables enterprises to connect their existing infrastructure to a set of isolated AWS compute resources via a Virtual Private Network (VPN) connection, and to extend
Keywords — Cloud Computing; Risk Management; Information Security; Cloud Risks; Software as a service; Platform as a service; Infrastructure as a service..
1) Protection from Data Breaches: Various security mea- sures and techniques have been proposed to avoid the data breach in cloud. One of these is to encrypt data before storage
Various attacks such as social engineering attack, XML signature wrapping attack, malware injection, data manipulation, account hijacking, traffic flooding, and wireless local
Plecândă deă laă explica iaă teoretic ă aă luiă Tonnies,ă putemă apreciaă c ă individulă voin eiăreflectateănuălucreaz ăînăfolosulăcomunit ii,ăaşaăcumăspuneăDimitrieăGustiă