An analysis of the alignment of the contracts for Cloud Computing with the norms and recommendations
Texto
Imagem

Documentos relacionados
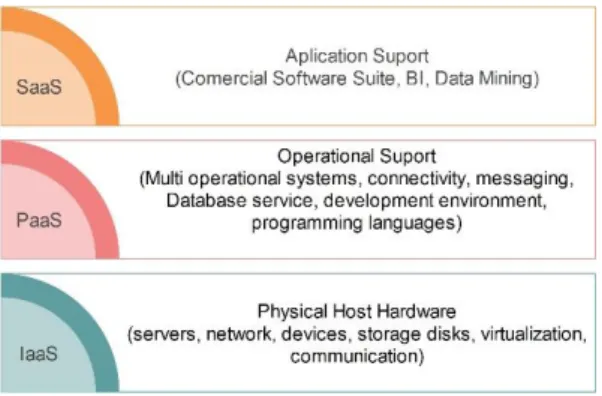
Cloud computing consist of three layers like Infrastructure as a service (Iaas) is a lowest layer, it provides the basic infrastructure support services, Platform as a service
It shares massively scalable, elastic resources (e.g., data, calculations, and services) transparently among the users over a massive network [3]. These opportunities, however,
Optimal cloud security practices should include encryption of sensitive data used by cloud- based virtual machines; centralized key management that allows the user
Cloud computing providers offer services built around three fundamental models: Infrastructure as a service (IaaS), platform as a service (PaaS), and software as a service
Another variant of role-based access control proposed for cloud computing environments is the Attribute-role-based access control (ARBAC) model [9], wherein the data
Another problem in cloud computing is that huge amount of logs make the system administarator hard to analyse them.In this paper we proposed the method that enables cloud
Amazon VPC enables enterprises to connect their existing infrastructure to a set of isolated AWS compute resources via a Virtual Private Network (VPN) connection, and to extend
The cloud computing security based on fully Homomorphic encryption, is a new concept of security which enables providing results of calculations on encrypted