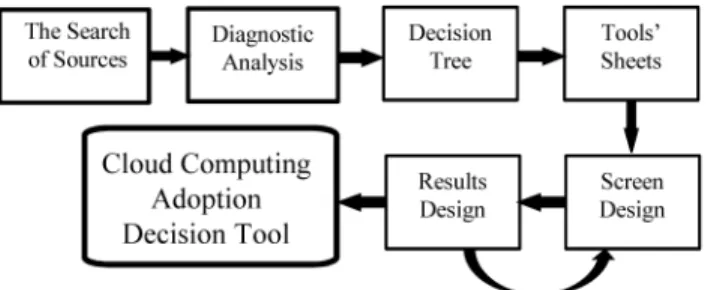
Design and Implementation of a Cloud Computing Adoption Decision Tool: Generating a Cloud Road.
Texto
Imagem
Documentos relacionados
Optimal cloud security practices should include encryption of sensitive data used by cloud- based virtual machines; centralized key management that allows the user
Fig. Overview of define Scope steps.. COBIT provides goals cascade to translate stakeholder needs into specific, actionable and customized enterprise goals and into IT
each one of the nodes received/issued. We tested 3 scenarios where 100 subscriptions with computation were submitted with a specified input tag , and the number of nodes in the cell
With this in mind, the cloud computing system (OpenStack) described in this chapter aims to provide the core features of a cloud computing architecture, On-demand self- service
It is shown that subgrid treatment of cloud activation and autoconversion of cloud water to rain reduce the impact of anthropogenic aerosols on cloud properties and thus reduce
Another problem in cloud computing is that huge amount of logs make the system administarator hard to analyse them.In this paper we proposed the method that enables cloud
This is just to show that we believe that this cloud layer should not belong to the category of very thin cloud layers, thus assuring that it will not be included in subsequent
Critical analysis of the responses elicited from the respondents with regards to whether CSR activities performed by MTN had an influence on their purchase decision of the