Impact of Malicious Nodes under Different Route Refresh Intervals in Ad Hoc Network
Texto
Imagem


Documentos relacionados
The elected cluster head will perform signature detection on all the member nodes along with running anomaly detection only on the backup node.. Similarly the backup will be
In an ad-hoc network that uses AODV as a routing protocol, a mobile node that wishes to communicate with other node first broadcasts an RREQ[6] (Route Request) message to find a
Já que “o poder maior do mito é sua recorrência” (BARTHES, 2001, p. 156) e representa “fonte dos textos e tramas da cultura” (CONTRERA, 1996), nossa proposição em
The Enhanced Reactive Dynamic Source Routing Algorithm Applied to Mobile Ad Hoc Networks (ERDSR) protocol is another variant of DSR algorithm that chooses the
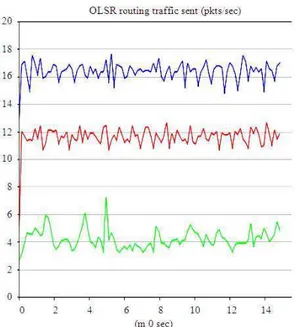
The protocol performance evaluation for an ad-hoc network is necessary to be tested under realistic conditions, especially including the movement of the mobile nodes which
if timeout period of sender node is x then timeout period of receiver node will be (x-m), where m will be critical factor. This factor [16] helps us to control the
Finally, it is being observed that the proposed RBDS using GKM has efficiently desgined for an effective communication in MANET using Group Key management
Routing is the critical issue in the MANET and focus based on routing protocols such as Ad hoc On-demand Distance Routing Protocol (AODV), Dynamic Source Routing (DSR),