SECURITY IN VEHICULAR AD HOC NETWORK BASED ON INTRUSION DETECTION SYSTEM
Texto
Imagem


Documentos relacionados
A presente diretiva pode igualmente dar uma importante contribuição para outros domí- nios de cooperação entre os Estados-Membros, nomeadamente para o Es- quema
than conventional SQL-based approach. In order to achieve 1 st research objective of RSECM, the proposed system first develops three different actors associated with the
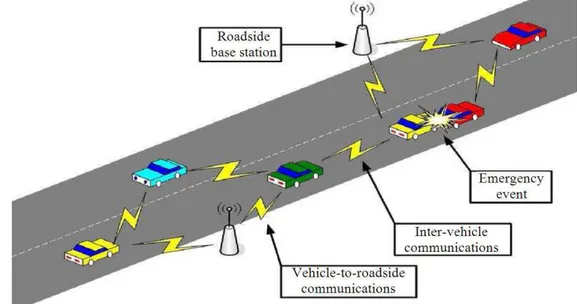
The elected cluster head will perform signature detection on all the member nodes along with running anomaly detection only on the backup node.. Similarly the backup will be
The rest of the paper is divided among the following sections: section 2 explains the existing passcode based technique which involves the matching process
Abstract: Accidents due to drowsiness can be controlled and prevented with the help of eye blink sensor using IR rays. It consists of IR transmitter and an IR receiver.
In this protocol, four concepts were combined: the collaboration between a sedentary agent and a mobile agent; the cryptography; the reference execution; the
The proper selection of clustering algorithm is critical to improve the detection rate of such a system to detect the routing attack; especially black hole attack in an
Based on our data, we believe that the multiplex approach to Ct detection is superior to commercial NAAT detection in that targeting multiple loci allows, in effect, a set of

